The post 2600 Magazine Offers $10K for Access to Donald Trump’s Tax Return appeared first on Social Hax.
The post 2600 Magazine Offers $10K for Access to Donald Trump’s Tax Return appeared first on Social Engineering Blogs.
We are offering $10K for 1st access to @realDonaldTrump’s tax return. Identity protected, PGP key at https://t.co/oU079zJ4YV [email protected]
— 2600 Magazine (@2600) September 28, 2016
Twitter users responded with several funny comments:
Assange rn@2600 @realDonaldTrump @wikileaks pic.twitter.com/IyNz2cFbvV
— Eating Machine (@emmajaniejones) September 28, 2016
@2600 Please tell me that when you release it, you’ll tell the press that it was obtained by “the hacker known as 4chin”
— John Shade (@John5hade) September 28, 2016
@2600 @realDonaldTrump. How about $10K for Hillary’s deleted e-mails?
— Jim (@TypeError_) September 28, 2016
“Hi IRS this is the real actual Donald Trump. I just wanted to make sure that my refund’s gonna be YOOOGE”
— r000t (@rootworx) September 28, 2016
There have been many recent attacks on the Democratic National Committee including the Guccifer 2.0/Wikileaks release of DNC emails and more recently a possible hack of some of the party member’s phones. Some say that hackers have been focusing too much on exposing the DNC and not enough on the RNC. Perhaps this is the opportunity they have been waiting for.
2600 has also extended the offer to Trump himself:
Incidentally, we will also pay @realDonaldTrump $10K if he gives us his tax return first. Or anyone in his campaign or family. Fair is fair.
— 2600 Magazine (@2600) September 28, 2016
The post 2600 Magazine Offers $10K for Access to Donald Trump’s Tax Return appeared first on Social Hax.
The post 2600 Magazine Offers $10K for Access to Donald Trump’s Tax Return appeared first on Social Engineering Blogs.
]]>The post Hackers Find Exploit and Reactivate LizardSquad’s Twitter Account appeared first on Social Hax.
The post Hackers Find Exploit and Reactivate LizardSquad’s Twitter Account appeared first on Social Engineering Blogs.
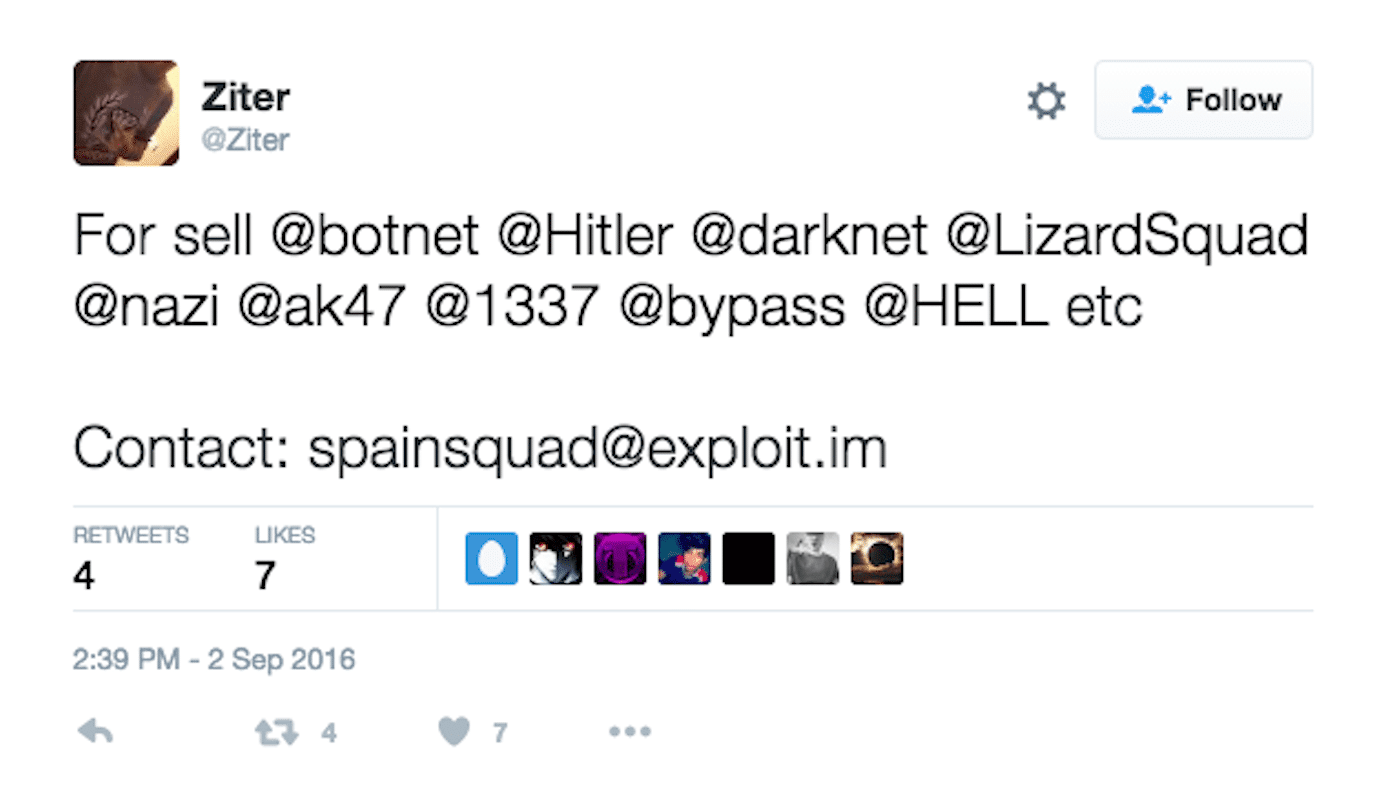
One of the hackers aligned with Spain Squad tweets about reactivated accounts.
“It could be a vulnerability in Twitter’s software, a compromised staff account, or some other explanation. It’s also unclear whether the exploit is still active, or was patched concurrently with the banning of the hijacked accounts.” (Business Insider)
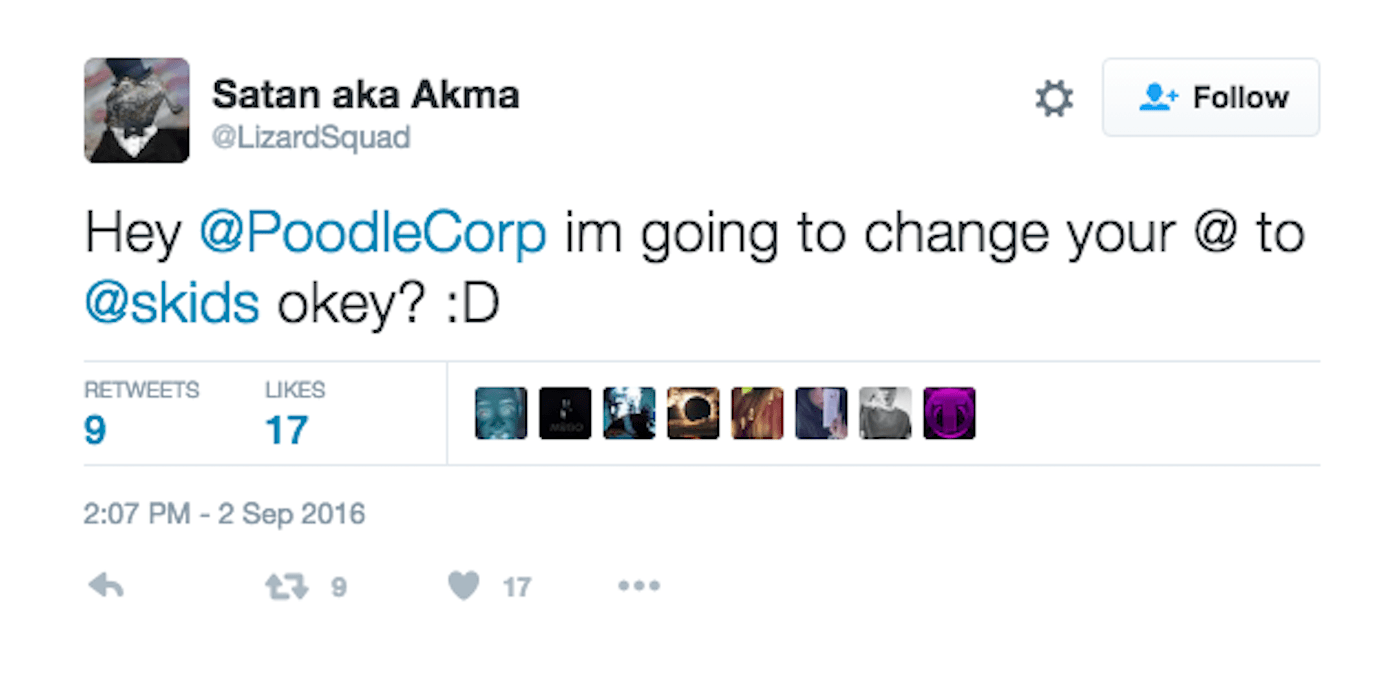
A spokesperson for the hacking group has stated they can do even more than recover old accounts with the exploit they found:
“The new exploit allows Spain Squad to change to suspend active accounts, change a user’s Twitter handle and even take control of active accounts. So far, the group has only demonstrated the ability to recover officially suspended accounts — though all of those have already been re-suspended by the social media company.” (Engadget)
Twitter actively suspends accounts that violate their Terms of Service (TOS). Sometimes these suspensions can be temporary and the user is able to restore their account after acknowledging broken rules and promising not to violate TOS again. Often, the user must delete offending tweets before the account will be restored. Alternatively, a Twitter account can become permanently suspended, which means the account is never to be restored under any circumstances. Restoring access to accounts that were thought to be never again accessible could prove to be profitable for hackers selling screen names that may be valuable. However Spain Squad claims to be non-malicious. Whatever their intent, they were definitely doing some of it for the lulz when they took control of the LizardSquad account:
The post Hackers Find Exploit and Reactivate LizardSquad’s Twitter Account appeared first on Social Hax.
The post Hackers Find Exploit and Reactivate LizardSquad’s Twitter Account appeared first on Social Engineering Blogs.
]]>The post Are The Shadow Brokers Like Snowden? Theory Suggests Insider Hack appeared first on Social Hax.
The post Are The Shadow Brokers Like Snowden? Theory Suggests Insider Hack appeared first on Social Engineering Blogs.
(Watch a quick overview about the NSA hack – “NSA Reportedly Hacked By Group Called The Shadow Brokers”):
Initially, evidence suggested that the Shadow Brokers were Russian, but a new theory is emerging that whoever is leaking this data might be “a second Edward Snowden… albeit one with different motives” (Fortune). James Bamfield, a journalist who is well known for his publications about United States intelligence agencies, believes that Russia would not want to publish these hacks if they obtained them, because companies would quickly patch their vulnerabilities and the information would soon be worthless to anyone trying to sell the data. He also brings up that the bad English used by the hackers seems to be phony. Furthermore, he suggests that the hacker(s) could be linked to the NSA’s Tailored Access Operations (TAO) which is a unit of the surveillance agency that gathers intelligence related to cyber-warfare. He states:
“Rather than the NSA hacking tools being snatched as a result of a sophisticated cyber operation by Russia or some other nation, it seems more likely that an employee stole them. Experts who have analyzed the files suspect that they date to October 2013, five months after Edward Snowden left his contractor position with the NSA and fled to Hong Kong carrying flash drives containing hundreds of thousands of pages of NSA documents.
So, if Snowden could not have stolen the hacking tools, there are indications that after he departed in May 2013, someone else did, possibly someone assigned to the agency’s highly sensitive Tailored Access Operations” (Reuters).
As of now, the “second Snowden” theory is just that – a theory. Most experts still say Russia is behind the hacks. Nevertheless, as Bamford puts it in his commentary – the “NSA may prove to be one of Washington’s greatest liabilities rather than assets.”
The post Are The Shadow Brokers Like Snowden? Theory Suggests Insider Hack appeared first on Social Hax.
The post Are The Shadow Brokers Like Snowden? Theory Suggests Insider Hack appeared first on Social Engineering Blogs.
]]>The post Hacker Steals User Data from Epic Games Forums appeared first on Social Hax.
The post Hacker Steals User Data from Epic Games Forums appeared first on Social Engineering Blogs.
An Epic Games Spokesperson says that passwords do not need to be changed for the Unreal Engine and Unreal Tournament forum but a “compromise of our legacy forums covering Infinity Blade, UDK, previous Unreal Tournament games, and archived Gears of War forums revealed email addresses, salted hashed passwords and other data entered into the forums. If you have been active on these forums since July 2015, we recommend you change your password on any site where you use the same password.”
Epic’s Forums were also hacked last year.
The post Hacker Steals User Data from Epic Games Forums appeared first on Social Hax.
The post Hacker Steals User Data from Epic Games Forums appeared first on Social Engineering Blogs.
]]>The post Did Another Hacker Steal NSA Exploits from the Shadow Brokers? appeared first on Social Hax.
The post Did Another Hacker Steal NSA Exploits from the Shadow Brokers? appeared first on Social Engineering Blogs.
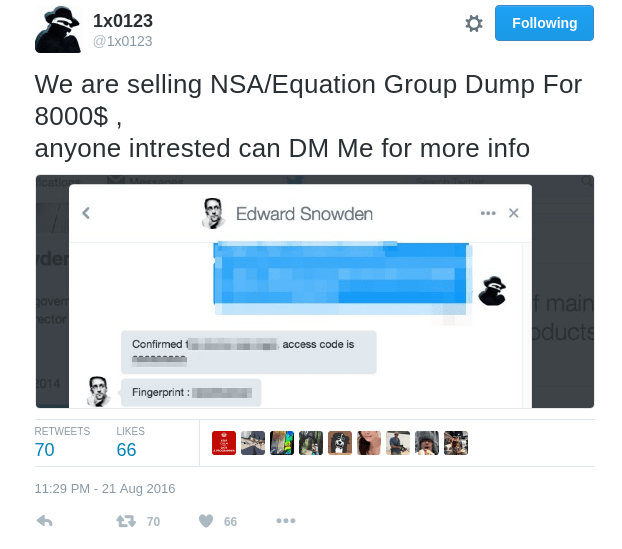
Gizmodo reached out to the hacker and were unable to verify their claims. However, back in April, NSA whistleblower Edward Snowden, gave them praise for reporting a vulnerability which may lend some credibility.
Thanks to @1×0123 for reporting a piwik vulnerability to @FreedomofPress! Great work. Got a bug report? Please contact @ageis with details.
— Edward Snowden (@Snowden) April 10, 2016
The hacker says they just need “some money to pay bills and stuff” and offered to share 50% of it with Gizmodo if they wanted to make an offer.
The post Did Another Hacker Steal NSA Exploits from the Shadow Brokers? appeared first on Social Hax.
The post Did Another Hacker Steal NSA Exploits from the Shadow Brokers? appeared first on Social Engineering Blogs.
]]>The post Facial Recognition gets “Hacked” Thanks to Facebook appeared first on Social Hax.
The post Facial Recognition gets “Hacked” Thanks to Facebook appeared first on Social Engineering Blogs.
University of North Carolina researchers have discovered a way to get around facial recognition security. By using a virtual reality (VR) system to develop 3D models of the face, they were able to trick the biometric security measures. They did this with just a handful of photos found on Facebook and were able to fool the systems more than half the time (Newsweek).
Clearly this is a huge security flaw in the technology which means other types of “verifiable data” would need to be used for authentication in order for facial recognition to be a feasible option. One technique that could be used is the detection of infrared radiation which would be given off by a real face, not a 3D model (Techworm).
For more information on how facial recognition technologies work, check out this video from Brit Lab:
The post Facial Recognition gets “Hacked” Thanks to Facebook appeared first on Social Hax.
The post Facial Recognition gets “Hacked” Thanks to Facebook appeared first on Social Engineering Blogs.
]]>The post A Seized Silk Road Wallet is Moving Bitcoin to the NSA Hackers appeared first on Social Hax.
The post A Seized Silk Road Wallet is Moving Bitcoin to the NSA Hackers appeared first on Social Engineering Blogs.
Now it appears that there are some Bitcoin moving from a seized Silk Road wallet to the Shadow Broker’s auction. This leads some experts to believe that “the US government is potentially bidding to prevent stolen NSA exploits and tools from ending up in the wrong hands”. It could also mean that the government might be making an attempt to trace where the Bitcoins are going. Additionally, it must be noted that the co-founder of a major Bitcoin investigation company says that payments are also going in the other direction. This could simply indicate that spam is being sent in very small payments to famous addresses. (ZDNet)
So far, the Shadow Brokers have collected around $1000 in Bitcoin payments – a far cry from the 1 million Bitcoins they have demanded (which would be worth just over a half a billion $USD at the time of this writing). The U.S. government seized several thousand Bitcoin when shutting down Silk Road, so this may be their source of funds when dealing with the Shadow Broker hackers.
Learn more about the Shadow Brokers hack of the NSA here:
The post A Seized Silk Road Wallet is Moving Bitcoin to the NSA Hackers appeared first on Social Hax.
The post A Seized Silk Road Wallet is Moving Bitcoin to the NSA Hackers appeared first on Social Engineering Blogs.
]]>The post NSA Hoards Zero Days; Doesn’t Disclose Them all to Vendors appeared first on Social Hax.
The post NSA Hoards Zero Days; Doesn’t Disclose Them all to Vendors appeared first on Social Engineering Blogs.
The US National Security Agency (NSA) was hacked by a suspected Russian hacker group and many of their exploits and hacking tools were archived. Leaked information was made public that showed the NSA collects exploits and does not always disclose them to vulnerable vendors. When vulnerabilities are not disclosed, problems do not get fixed. The NSA appears to operate “on the premise that secrets will never get out. That no one will ever discover the same bug. That no one will ever use the same bug. That there will never be a leak” (Business Insider).
Unfortunately, as we are currently witnessing with this recent leak, other types of hackers are able to find the same bugs and those hackers could have more malicious intent than the NSA. When hackers obtain a trove of U.S. secrets, that could put the government and corporations worldwide in a susceptible position. For example, the leaked data includes information on breaching popular commercial firewalls. Emergency service providers, governments, financial systems and many businesses all rely on these firewall technologies.
Global networking company, Cisco Systems, confirmed last week that the NSA exploited an undetected severe vulnerability that allows remote attackers “who have already gained a foothold in a targeted network to gain full control over a firewall” (Ars Technica). The NSA knew about this vulnerability since 2013 and did nothing to stop it. Now that the data is leaked, Cisco fears that the information “could be used to breach its Adaptive Security Appliance (ASA) software used in its firewalls. An exploit could allow the attacker to execute arbitrary code and obtain full control of the system or to cause a reload of the affected system”. It can be argued that these exploits would have been patched had the NSA disclosed the vulnerabilities instead of collecting them for their own use.
(Watch – Snowden discusses NSA hack, Cisco to cut 5,500 jobs, NASA preps an asteroid rocket):
The post NSA Hoards Zero Days; Doesn’t Disclose Them all to Vendors appeared first on Social Hax.
The post NSA Hoards Zero Days; Doesn’t Disclose Them all to Vendors appeared first on Social Engineering Blogs.
]]>The post Study Suggests Gamers Have Better Academic Performance appeared first on Social Hax.
The post Study Suggests Gamers Have Better Academic Performance appeared first on Social Engineering Blogs.
One argument can be made that gamers tend to do better in school because smarter kids might be more likely to play games than others (correlation does not equal causation). Additionally, kids that played games every single day without any breaks in between actually did worse on the academic tests.
The idea that gamers are smarter is nothing new. In 2004, SourceFed released a video titled “16 Ways Video Games Make You Smarter” which discusses research that demonstrates video games actually improve cognitive skills:
A similar study last year determined that gamers have more grey matter and better brain connectivity (Science Alert). Gaming can have beneficial effects on your brain such as hand-eye coordination and improved cognitive control. It is worth noting that other tasks that require skill like sports and art will have a similar effect on brain development.
The post Study Suggests Gamers Have Better Academic Performance appeared first on Social Hax.
The post Study Suggests Gamers Have Better Academic Performance appeared first on Social Engineering Blogs.
]]>The post Many Fans Illegally Download Frank Ocean’s #Blond Album appeared first on Social Hax.
The post Many Fans Illegally Download Frank Ocean’s #Blond Album appeared first on Social Engineering Blogs.
Because other popular streaming services such as Spotify and Tidal are unable to stream Blonde, those who are not subscribers to Apple’s service have had to find other means of obtaining the album. A quick Google search has also led some listeners to file locker locations containing the album files. Some Reddit threads have links to file hosting sites like Zippyshare to help share the album more widely.
Since Blonde was released exclusively to Apple Music, some have signed up for the service specifically to hear the album:
I don't fuck with Apple Music #, but I'll do it for you Frank #Blonde #FrankOcean
— Rosicella Luna (@chihuahuarosi) August 21, 2016
#Blonde you know what fuck it in using my free 3 moth trial on Apple Music this is an emergency
— #BLM (@miamia697) August 21, 2016
Welp I caved in and subscribed to Apple Music, and it was so worth it. #Blonde #FrankOcean #Masterpiece
— Ali Philippides (@ClubAliP) August 21, 2016
I just made a whole new apple ID just for a free trial of Apple Music #Blond
— grace keller (@graceakell) August 21, 2016
Others are promoting pirating the album for those who don’t want to pay or sign up for Apple Music:
@FrankOcean FOR ALL MY NIGGAZ WHO DONT WANNA PAY FOR THIS –> https://t.co/6mCybw6vT1 #FRANKOCEAN #BLONDE
— JUULDELATOERET (@juuldelatoeret) August 21, 2016
i'm against piracy but when it's ocean i resort to torrenting #Blonde
— Alec Xavier (@axemfirst) August 21, 2016
Having given exclusive rights to Apple Music, the Frank Ocean brand has gone against Kim Dotcom’s suggestions for stopping piracy:
How to stop piracy:1. Create great content2. Make it easy to buy3. Same day global release4. Works on any device5. Fair price
— Kim Dotcom (@KimDotcom) September 19, 2013
By not making the album easy to buy or obtain, many people feel that piracy is a better option for those who are not subscribers to Apple Music.
The post Many Fans Illegally Download Frank Ocean’s #Blond Album appeared first on Social Hax.
The post Many Fans Illegally Download Frank Ocean’s #Blond Album appeared first on Social Engineering Blogs.
]]>